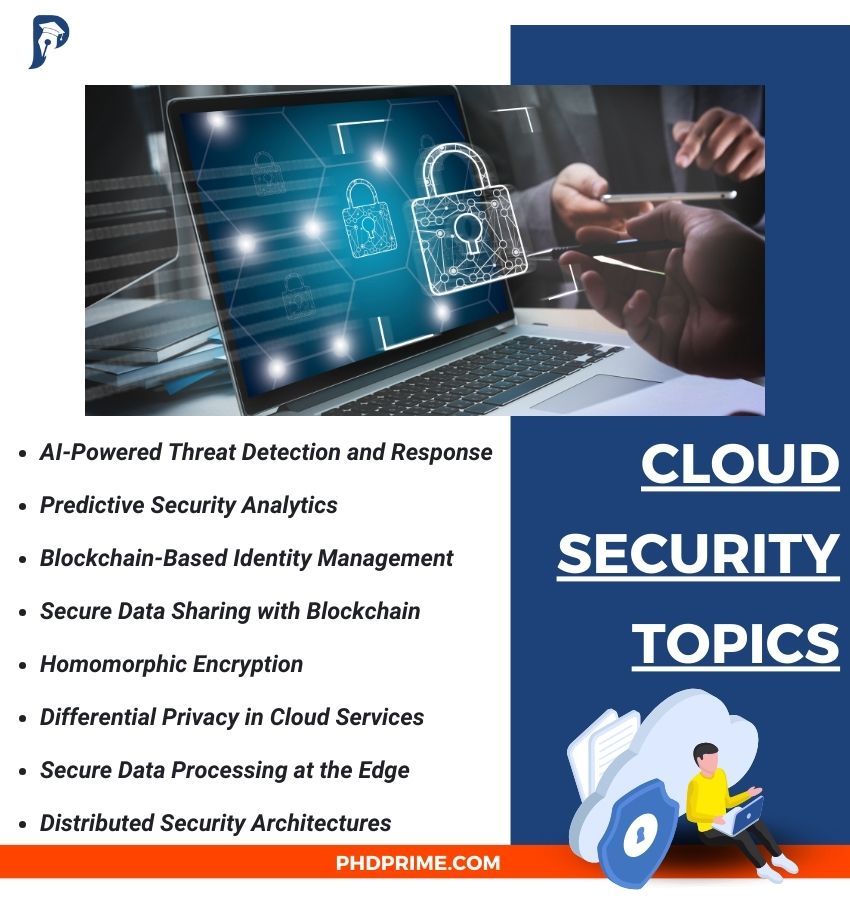
Cloud security is an efficient approach which aims to secure different cloud-based frameworks and data from several attacks and threats. It also offers robust security mechanisms, tools, and methods for various purposes. Regarding cloud security, we suggest numerous significant and current topics that are appropriate for 2025:
- Quantum-Resistant Security
Post-Quantum Cryptography
- Explanation: To protect from quantum computing assaults, create efficient cryptographic methods.
- Goal: In cloud platforms, apply and regularize quantum-resistant methods.
Quantum Key Distribution (QKD) in Cloud
- Explanation: In order to attain secure key sharing in cloud services, utilize QKD.
- Goal: Improve data security through the incorporation of QKD into the previous cloud security framework.
- AI-Driven Security Solutions
AI-Powered Threat Detection and Response
- Explanation: For actual-time identification and response to security hazards, use machine learning and AI.
- Goal: Optimize response times and reduce false positives through improving the effectiveness and preciseness of AI frameworks.
Predictive Security Analytics
- Explanation: To forecast possible security violations, utilize predictive analytics.
- Goal: Predict and reduce upcoming hazards by employing machine learning frameworks and previous data.
- Blockchain and Decentralized Security
Blockchain-Based Identity Management
- Explanation: Through the utilization of blockchain, the decentralized identity management systems have to be applied.
- Goal: By means of secure, decentralized identity validation, improve confidentiality and safety.
Secure Data Sharing with Blockchain
- Explanation: Among several cloud providers, assure reliable and safer data exchange by employing blockchain mechanisms.
- Goal: To handle data morality and access control, use unchangeable ledgers and smart contracts.
- Privacy-Preserving Technologies
Homomorphic Encryption
- Explanation: As a means to secure data confidentiality, facilitate computations on encrypted data, excluding the decryption process.
- Goal: Appropriate for realistic cloud applications, the effective homomorphic encryption policies must be created.
Differential Privacy in Cloud Services
- Explanation: While supporting the data analysis process, secure the confidentiality of personal data through implementing differential privacy approaches.
- Goal: To assure privacy-preserving data analytics in different cloud services, use differential privacy.
- Edge and Fog Computing Security
Secure Data Processing at the Edge
- Explanation: At fog and edge nodes, assure safer data storage and processing.
- Goal: Specifically for resource-limited edge devices, create lightweight safety protocols.
Distributed Security Architectures
- Explanation: For fog and edge computing platforms, apply distributed security architectures.
- Goal: In decentralized systems, attain data morality, accessibility, and privacy by improving security approaches.
- Zero Trust Architecture
Implementing Zero Trust in Cloud Environments
- Explanation: Improve cloud security through implementing a zero trust security framework.
- Goal: To assure safer access control, validate each access request in a consistent manner irrespective of its source.
Micro-Segmentation
- Explanation: To restrict the effect of security violations, the cloud platform has to be partitioned into concise phases.
- Goal: In order to improve threat control and isolation, apply micro-segmentation approaches.
- Advanced Threat Detection and Mitigation
Behavioral Analytics for Insider Threat Detection
- Explanation: Identify and reduce insider threats by employing behavioral analytics.
- Goal: To detect and react to malicious actions, track user behavior trends.
Automated Incident Response
- Explanation: Identify and respond to incidents in actual-time through creating automatic systems.
- Goal: For detecting, examining, and reducing security incidents in an automatic manner, utilize machine learning and AI.
- IoT Security in Cloud
Secure IoT Device Onboarding
- Explanation: In cloud platforms, assure safer authentication and deployment for IoT devices.
- Goal: Plan to apply safer bootstrapping techniques and certificate-based authentication.
Lightweight Encryption for IoT
- Explanation: To carry out safer data sharing from IoT devices to the cloud platform, create lightweight encryption protocols.
- Goal: In resource-limited IoT platforms, assure protective and effective interaction.
- Regulatory Compliance and Data Sovereignty
Automated Compliance Management
- Explanation: For consistent compliance tracking and handling, consider the creation of automatic tools.
- Goal: The cloud services must be adhered to emerging regulatory principles and needs. Assuring this aspect is significant.
Data Sovereignty and Localization
- Explanation: Aim to assure adherence to regional data security rules and handle data sovereignty needs.
- Goal: To preserve data localization and manage cross-border data sharing, apply efficient policies.
- Cloud-Native Security Solutions
Security for Serverless Architectures
- Explanation: In serverless computing platforms, solve issues relevant to safety.
- Goal: Handle access controls, protect event triggers, and assure function isolation in serverless applications.
Container Security
- Explanation: The safety of containerized platforms and applications has to be improved.
- Goal: For container orchestration environments such as Kubernetes, apply efficient security approaches.
- Secure Multi-Cloud and Hybrid Cloud Environments
Multi-Cloud Security Management
- Explanation: Particularly for multi-cloud placements, create extensive security policies.
- Goal: Among several cloud environments, assure continuous threat identification, response, and security strategies.
Hybrid Cloud Security Solutions
- Explanation: For hybrid cloud platforms, which combine cloud resources and on-sites, improve security approaches.
- Goal: While assuring appropriate combination, handling security among various frameworks is crucial.
- Compliance as Code (CaC)
Implementing Compliance as Code
- Explanation: Utilize code to automate compliance analysis and implementation.
- Goal: Focus on assuring that the continuous integration/continuous deployment (CI/CD) pipelines and infrastructure as code (IaC) adhere to regulatory and safety principles.
Continuous Compliance Monitoring
- Explanation: For compliance tracking and automatic recovery in actual-time, create robust tools.
- Goal: By means of automatic analysis and warnings, consistent respect for compliance needs has to be assured.
What are the Problems and solutions in cloud security?
In the approach of cloud security, several issues exist based on external hazards and various types of attacks. Related to cloud security, we list out a few general issues, along with possible solutions to address them:
- Data Breaches
Issue:
Risks in cloud services and storage can cause data violations, which result in leakage of confidential data and illicit access.
Possible Solutions:
- Encryption: For data at transmission and inactive state, utilize robust encryption techniques. Encryption keys must be handled in a safer manner and assuring this aspect is important.
- Access Controls: It is significant to assure that only legal users have permission to use confidential data. Plan to apply efficient access controls.
- Regular Audits: To detect and reduce possible risks, carry out risk evaluations and security analysis frequently.
- Insufficient Identity and Access Management (IAM)
Issue:
Mishandling and illicit access of cloud resources can be resulted through the inefficient IAM approaches.
Possible Solutions:
- Multi-Factor Authentication (MFA): Over passwords, include an extra layer of security by applying MFA.
- Role-Based Access Control (RBAC): To conduct specific missions, assure that the users have very less required permissions. For that, employ RBAC.
- Regular Reviews: Assure that the access permissions and roles are advanced by frequently upgrading and analyzing them.
- Data Loss
Issue:
Various problems like natural disasters, hardware faults, or accidental deletion can lead to data loss.
Possible Solutions:
- Regular Backups: For important data, apply automatic and frequent backups.
- Redundant Storage: To assure data is copied among several locations, utilize redundant storage systems.
- Disaster Recovery Plans: Assure rapid recovery at the time of data loss by creating and assessing extensive disaster recovery strategies.
- Insider Threats
Issue:
Unintentional or targeted data violations can occur through insider threats especially from dealers or workers.
Possible Solutions:
- Behavior Monitoring: In order to identify abnormal actions which might be the sign of insider threats, employ user behavior analytics.
- Least Privilege Principle: To perform missions, make sure that the workers have a minimum requirement of permissions.
- Security Training: Workers must have expertise based on possible hazards and efficient approaches. So, aim to offer security training to them frequently.
- Insecure Interfaces and APIs
Issue:
To destroy services or accomplish illicit access, assaulters can employ unsafe APIs.
Possible Solutions:
- Secure Development Practices: Along with security efficient approaches such as authentication and input validation, the APIs have to be created. Assuring this factor is significant.
- API Gateway: To handle API traffic and implement security strategies, utilize API gateways.
- Regular Testing: To detect and mitigate risks, perform frequent security analysis, like code analysis and penetration testing.
- Misconfiguration and Inadequate Change Control
Issue:
Data can be leaked to illicit access, due to the mis-arrangements of cloud resources. It can also result in significant risks.
Possible Solutions:
- Automated Tools: To analyze and rectify mis-arrangements, employ automatic tools.
- Configuration Management: Monitor and handle modifications to cloud resources by applying efficient configuration management procedures.
- Security Posture Management: As a means to track and enhance cloud security arrangements, utilize cloud security posture management (CSPM) tools.
- Lack of Visibility and Monitoring
Issue:
Identification and response to security phenomena can be challenging, because of inadequate visibility into cloud platforms.
Possible Solutions:
- Centralized Logging: In order to gather and examine records from all cloud resources, apply centralized logging.
- Continuous Monitoring: For the actual-time identification and response to security phenomena, employ continuous tracking tools.
- Security Information and Event Management (SIEM): Among the cloud platforms, collect and examine security data through the utilization of SIEM systems.
- Compliance and Regulatory Issues
Issue:
In cloud platforms, it can be highly difficult to assure adherence to different principles and rules.
Possible Solutions:
- Compliance Automation: Assure adherence to major principles and rules by employing automatic tools.
- Regular Audits: To detect and solve gaps, carry out compliance analysis frequently.
- Documentation: Based on compliance techniques and security approaches, keep an extensive documentation.
- Denial of Service (DoS) Attacks
Issue:
Assaults based on DDoS can lead to downtime and destroy cloud services.
Possible Solutions:
- Rate Limiting: Obstruct unnecessary requests from enormous services through utilizing rate limiting technique.
- DDoS Protection Services: To reduce assaults, the DDoS protection services have to be implemented, which are suggested by cloud providers.
- Scalable Architecture: For analyzing and reducing the effect of DoS assaults, model adaptable cloud frameworks.
- Third-Party Risks
Issue:
Security vulnerabilities can be presented through the combination of external services and dealers with the cloud platforms.
Possible Solutions:
- Vendor Risk Management: On the basis of external dealers and their services, carry out in-depth security evaluations.
- Contractual Agreements: In contracts with external dealers, encompass SLAs and security necessities.
- Continuous Monitoring: For security concerns and adherence, track external services in a consistent manner.
- Lack of Cloud Security Expertise
Issue:
To protect cloud platforms in an efficient manner, firms might not have adequate knowledge.
Possible Solutions:
- Training and Certification: To develop knowledge based on cloud security, introduce certification and training courses for IT employees.
- Managed Security Services: For enhancing in-house security proficiencies, utilize managed security service providers (MSSPs).
- Security Best Practices: From cloud providers and industry entities, consider the current cloud security instructions and efficient approaches, and remain upgraded accordingly.
Latest Cloud Security Topics 2025
The Latest Cloud Security Topics 2025 that we have worked are stated below. We have provided more than 7000+ successful projects on cloud security we abide by your university guidelines and finish of your work in time.
- Self-Adaptive and Resource-Efficient SLA Enactment for Cloud Computing Infrastructures
- A novel methodology for security and privacy of cloud computing and its use in e-Governance
- Load balancing algorithms in cloud computing: A survey of modern techniques
- Enhanced Active Monitoring Load Balancing algorithm for Virtual Machines in cloud computing
- UAA: User authentication agent for managing user identities in cloud computing environments
- The Analysis and Implementation of Index Management System Based on Cloud Computing
- The Implementation of Prioritized Task Scheduling for VOIP Data Package Processing in Cloud Computing
- Categorizing hardware failure in large scale cloud computing environment
- HMCC: A Hybrid Mobile Cloud Computing Framework Exploiting Heterogeneous Resources
- SIaaS – Sensing Instrument as a Service Using Cloud Computing to Turn Physical Instrument into Ubiquitous Service
- Comparison of cluster, Grid and Cloud Computing using three different approaches
- Trusted Access Control Model Based on Role and Task in Cloud Computing
- Load Prediction for Energy-Aware Scheduling for Cloud Computing Platforms
- Job Scheduling for Cloud Computing Integrated with Wireless Sensor Network
- QoS-Aware Data Replication for Data-Intensive Applications in Cloud Computing Systems
- Energy-aware and real-time service management in cloud computing
- Performance-Based Pricing in Multi-Core Geo-Distributed Cloud Computing
- Biometrie based authentication and access control techniques to secure mobile cloud computing
- Design and implementation of an SLA and energy-aware VM placement policy in green cloud computing
- Energy Efficient Load Balancing Algorithm through MetaHuristics Approaches for Cloud-Computing-Environment





















